How to use incident response playbooks to build customer trust
Discover how B2B teams use incident response playbooks to communicate clearly, align on strategies, and build customer trust during critical moments.
You never really want to encounter incidents like security breaches or platform outages, but these situations are an opportunity to build trust with customers. With a well-designed, customer-focused incident response playbook, you can turn these moments into success stories that deepen the customer relationship.
This article covers what makes a good incident response playbook, including how to focus on customer trust, align the whole team around mitigation tactics, and scale and improve playbooks over time.
What’s a customer-centric incident response playbook?
An incident response playbook is a detailed guide for teams to follow when a serious incident occurs. Although they often deal with cybersecurity incident management, playbooks can also cover other major operational issues like server outages, database failures, product recalls, and compliance issues.
While a traditional cybersecurity playbook focuses on technical steps to respond to a phishing attack or data breach, a customer-centric incident response playbook puts the emphasis on maintaining customer trust. It’s less about internal operations and more about proactive, consistent communication to build trust and protect customer relationships.
Also, while an incident response plan lays out the overall strategy for handling incidents, a playbook gives clear steps, scenarios, and workflows for your team to follow in specific situations. A company usually has multiple incident response playbooks that cover different types of events.
Core components of a trust-building incident response playbook
These are the most important elements to include in a customer-focused incident response playbook:
- Incident detection and classification. Define the kinds of events that call for incident response; not every issue requires escalation or use of a playbook. Set criteria your team can use to classify incidents by severity and impact.
- Roles and responsibilities. Clarify who will manage the incident response, assigning specific members of different teams to lead different areas. For example, you’ll need someone from your customer support team to be responsible for customer communication, a dev team representative to manage the technical response, and a customer success manager to handle proactive outreach to high-value accounts.
- Incident response procedures. Set out clear workflows for your team to follow when a major incident occurs. Specify the process for escalating support tickets, how the teams will collaborate to resolve them, how the fix will be tested, how to manage containment and eradication of security threats, and how to keep customers informed. Clarify when and how the team can use AI tools to assess and prioritize incidents and formulate responses.
- Communication and stakeholder updates. Create a plan for how you’ll communicate with customers, from initial customer broadcasts that have details of the issue to regular follow-ups and personalized check-ins with high-value accounts. Help your team understand how much detail they should share with customers, and how they can communicate with honesty and empathy. Make sure you communicate often, even if there’s nothing new to report — this builds trust and ensures customers don’t have to contact you to ask for updates.
- Post-incident review and improvement. Document what happened, why it happened, and how you’ll try to reduce the risk of it happening again. Also examine your response, checking your customer support KPIs during the incident and making improvements to your incident response playbook where needed.
How to build incident response playbooks: 5 steps
Work with all relevant leadership teammates to build out your customer support-focused incident response playbooks.
1. Map customer impact and risk scenarios
Create a list of all the issues that could seriously affect your customers (security vulnerabilities, server outages, system failures, data breaches, compliance issues, etc.). Categorize them by customer impact (how seriously they will affect your customers and their ability to use your products) and risk (how likely they are to happen).
Then, prioritize each type of incident. These are some common categories:
- P1: High priority, all customers or key accounts seriously affected
- P2: Medium priority, limited scope or impact
- P3: Low priority, minimal disruption to customers
2. Define ownership across support, engineering, and CS
For each type of incident, define who will be responsible in each team. Quick action is important, and your team needs to know exactly who to contact and what they’re personally accountable for.
At a minimum, include:
- Customer support for ticket management, quick responses, and proactive customer updates
- Engineering for technical investigation, containment, and resolution
- Customer success for personalized outreach to key customers
Think through every scenario and bring in other teams when you need to, with clear ownership at every stage. And define escalation protocols based on incident severity.
3. Create structured communication workflows
Decide on the best channels for internal and external communication during the incident. Specify the frequency of communication with customers depending on how serious the incident is. For instance, you might give those affected by high-priority (P1) incidents updates every half an hour, and you could give hourly updates for P2 incidents.
Important: Do your best to avoid conflicting messages during an incident — this is a quick way to confuse customers and potentially lose their trust. Clearly define who will communicate to which accounts and what information they can share.
Make it easy for your team to communicate by giving them templates for common stages like:
- Incident announcement
- Half-hourly updates
- Resolution announcement
- Post-incident follow-up
4. Build repeatable playbooks for common incidents
Give your team step-by-step instructions to help them respond consistently and fix critical issues promptly. Keep the instructions simple so that they’re easy to follow in high-pressure situations. Things like flow charts, decision trees, and checklists work well.
Make sure you cover every stage of the incident, from identification and logging in the ticketing system through to escalation, investigation, containment, resolution, and post-incident review.
5. Close the loop with reviews and customer follow-ups
Once the incident has been resolved, customer follow-ups are a must. The main purpose is to make sure that every customer is back online and experiencing normal service, but these follow-ups are also a great way to build customer trust by showing you care about how they were affected, even once the issue is resolved.
You could also collect feedback during this time, either casually during a check-in call or via a customer survey.
Real-world incident playbook examples for customer-facing teams
Here are a few examples of companies that turned incidents into opportunities via customer-focused incident responses:
- In 2024, Slack was hit by a major outage that threatened its reputation, but its support team acted quickly to minimize frustration. They acknowledged the issue, reassured customers that they were working on it, and posted frequent updates using empathetic, honest language. Once the issue was resolved, they published a review to explain what happened. It’s a textbook example of a customer-focused incident response playbook in action.
- Financial services firm Société Générale made its security incident response playbooks available on GitHub for anyone to view and use. The large number of playbooks covering various cybersecurity scenarios shows how seriously the company takes its customers’ security.
- Shipping company Maersk faced a ransomware attack in 2017 that caused a major outage. Maersk quickly switched from its usual computerized systems to manual, paper-based processes, which meant it could start accepting bookings from existing customers while it took systems offline and worked on making them safe. By quickly switching to a backup system, Maersk minimized the impact of the outage on its customers and preserved account relationships.
Scaling and continuously improving your incident playbooks
As your company grows — maybe you change your org structure or add new teams — you’ll need to update your incident response playbooks. Set a reviewal cycle of about 4 to 6 months where a reviewal team reviews the playbooks and makes sure they reflect company and account changes. You might just manually review, or test each playbook to make sure it still makes sense.
Also, refine your playbook after each incident to take account of processes that went well and those that didn’t. Collect feedback from those involved (both employees and customers), and update the playbook to reflect these insights.
Put customers first in your incident response playbook
Every company needs to be prepared for incidents. With a thoughtful, customer-centric incident response playbook, incident management becomes a chance to build trust with customers. This is especially true if you use an all-in-one B2B support platform that centralizes the account information you need to effectively update customers.
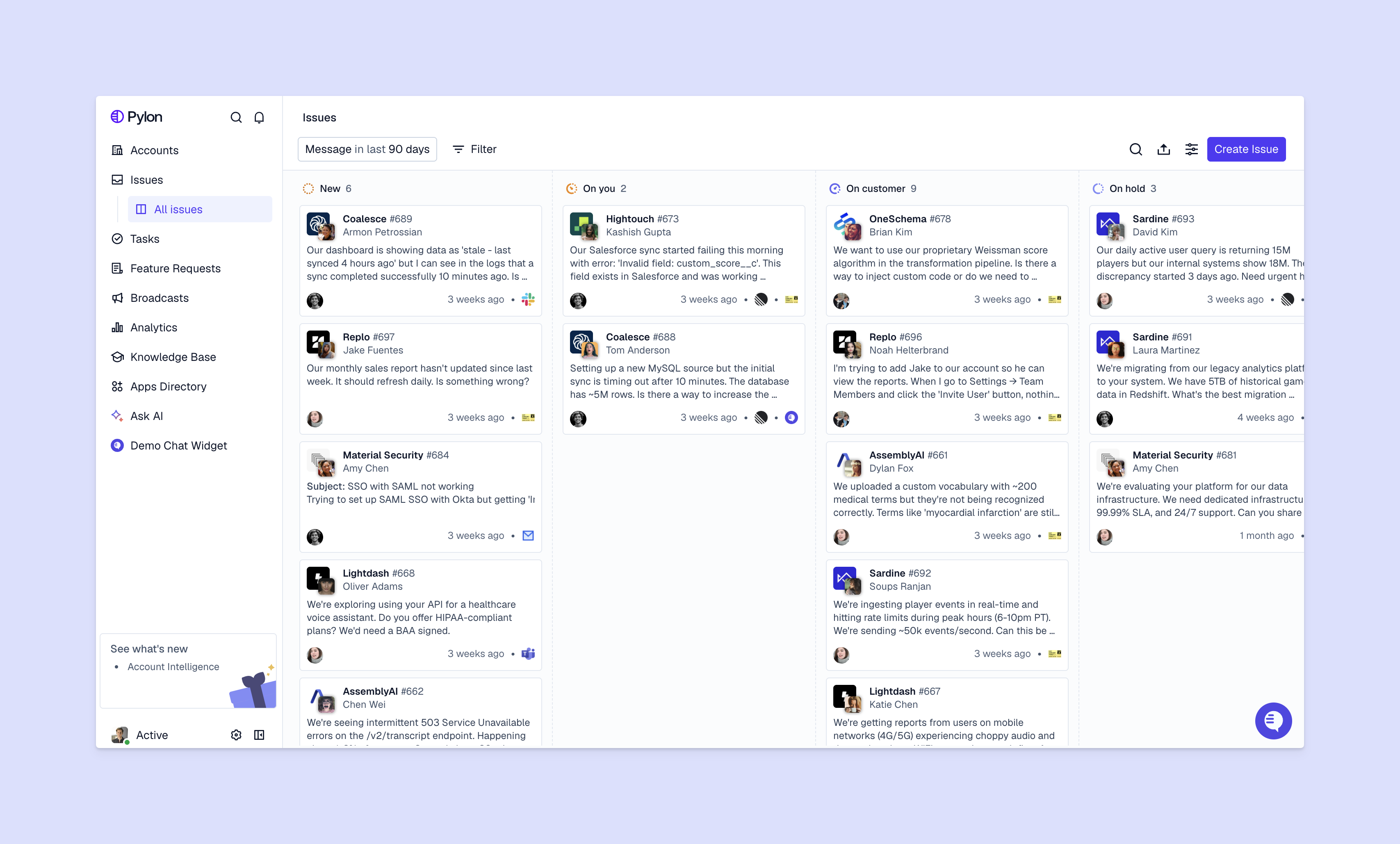
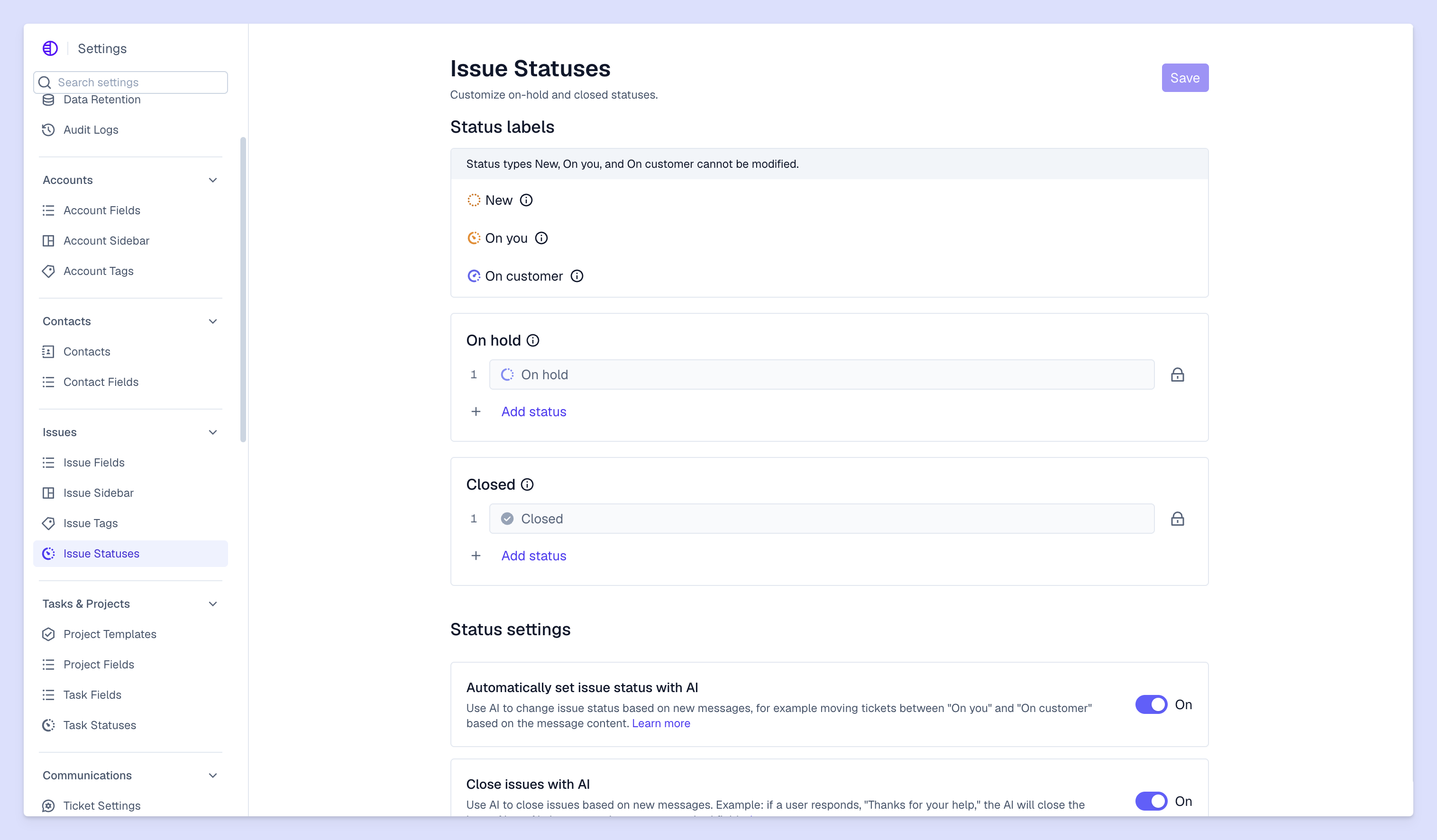
Pylon is the modern B2B support platform that offers true omnichannel support across Slack, Teams, email, chat, ticket forms, and more. Our AI Agents and Assistants automate busywork and reduce response times. Plus, with Account Intelligence that unifies scattered customer signals to calculate health scores and identify churn risk, we're built for customer success at scale.
FAQ
How is a customer-focused incident response playbook different from a traditional one?
A customer-focused playbook prioritizes communication, context, and experience — not just technical resolution. It defines how teams explain issues, set expectations, and maintain trust while an incident is being resolved.
Who should be involved in customer incident response beyond the support team?
Effective playbooks typically include support, engineering, product, customer success, and leadership. Trust is built when customers experience consistent messaging and coordinated action across every team they interact with.
How do you maintain transparency with customers without over-sharing during incidents?
The key is structured communication: clear updates, realistic timelines, and plain-language explanations. A strong playbook defines what to share, when to share it, and how to tailor messaging by customer impact.










